Introduction
In the rapidly evolving landscape of artificial intelligence operations (AIOps), the integration of machine learning operations (MLOps) has become increasingly essential. As organizations leverage AI to automate IT operations, ensuring the security of MLOps pipelines is paramount. This tutorial provides a step-by-step guide for building a secure MLOps pipeline tailored to AIOps environments, emphasizing data security, model management, and compliance.
Security in MLOps is not just a technical necessity; it’s a strategic imperative. With the proliferation of data breaches and cyber threats, safeguarding your pipeline is crucial to maintain trust and operational integrity. This guide aims to equip data engineers, security analysts, and MLOps practitioners with the knowledge needed to secure their pipelines effectively.
Understanding the MLOps Pipeline
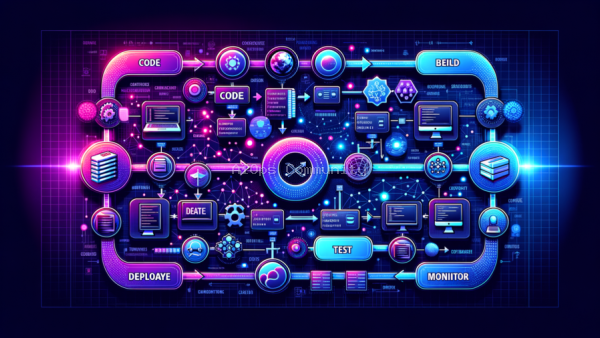
The MLOps pipeline is a workflow that manages the lifecycle of machine learning models from development to deployment. It integrates various stages such as data collection, model training, validation, deployment, and monitoring. In the context of AIOps, this pipeline must be agile yet secure to handle the dynamic nature of IT operations data.
Key components of the MLOps pipeline include data ingestion, preprocessing, model training, and deployment. Each of these stages presents unique security challenges that need to be addressed to protect sensitive information and ensure compliance with industry standards.
Before diving into security measures, it’s important to map out your existing pipeline. Identify potential vulnerabilities and areas where security enhancements can be integrated seamlessly.
Securing the Data
Data is the foundation of any MLOps pipeline. Ensuring its security involves both preventing unauthorized access and maintaining data integrity. Implementing robust access controls and encryption protocols are essential first steps.
- Access Controls: Use role-based access controls (RBAC) to ensure that only authorized personnel have access to sensitive data. This minimizes the risk of insider threats and unauthorized data exposure.
- Encryption: Encrypt data both at rest and in transit using industry-standard encryption algorithms. This ensures that even if data is intercepted, it remains unreadable without the appropriate decryption keys.
- Data Masking: For environments where data needs to be shared for analysis or development, consider using data masking techniques to obfuscate sensitive information while retaining its utility.
Model Management Security
Once data is secure, focus shifts to the models themselves. Models can be vulnerable to adversarial attacks and data poisoning, which can compromise their accuracy and reliability.
- Version Control: Implement version control for models to track changes and roll back to previous versions if needed. This is critical for maintaining a history of model changes and identifying potential sources of errors or vulnerabilities.
- Adversarial Testing: Conduct adversarial testing to identify potential vulnerabilities in your models. This involves simulating attacks to understand how models respond and reinforcing them against such threats.
- Secure Deployment: Use containerization and orchestration tools like Docker and Kubernetes to securely deploy models. These tools offer built-in security features that help isolate models and manage resource allocation efficiently.
Compliance and Monitoring
Compliance with industry standards and regulations is a cornerstone of a secure MLOps pipeline. Regular audits and continuous monitoring are necessary to ensure ongoing compliance and security.
- Regulatory Compliance: Stay informed about relevant regulations such as GDPR, HIPAA, or CCPA, and ensure that your pipeline adheres to these standards. This includes maintaining detailed records of data processing activities and obtaining necessary consents.
- Continuous Monitoring: Implement monitoring tools to track the performance and security of your pipeline in real-time. Anomalies can be detected early, allowing for quick remediation before they escalate into significant issues.
- Incident Response Plan: Develop and maintain an incident response plan to address security breaches or compliance violations promptly. This should include predefined roles, responsibilities, and communication protocols.
Conclusion
Building a secure MLOps pipeline in AIOps is an ongoing process that requires vigilance, adaptation, and commitment to best practices. By securing data, managing models efficiently, and ensuring compliance, organizations can protect their investments and foster trust in AI-driven operations.
As the landscape of AIOps continues to evolve, the importance of a secure MLOps pipeline cannot be overstated. By following the steps outlined in this tutorial, practitioners can build a robust foundation that not only safeguards their operations but also empowers them to innovate with confidence.
Written with AI research assistance, reviewed by our editorial team.